Salesforce Shield, a component of Salesforce Platform, is a security solution that secures your company with point-and-click capabilities to improve transparency, governance, trust, and compliance across all essential applications and systems. According to the system, as more businesses and individuals use Salesforce to store sensitive data, effective processes are required to satisfy internal and external regulatory compliance needs. The method comprises four parts: event monitoring, platform encryption, field audit trail, and data archive. These components work together to take compliance and trust to the next level, allowing you to monitor data and app usage, encrypt critical information, execute compliance audits, and automate security rules.

Salesforce Shield is basically a set of security solutions that allows you to incorporate additional layers of trust, compliance, and governance into your mission-critical apps. Shield Platform Encryption, Event Monitoring, and Field Audit Trail are all included. Inquire with your Salesforce administrator if Salesforce Shield is available in your organization.
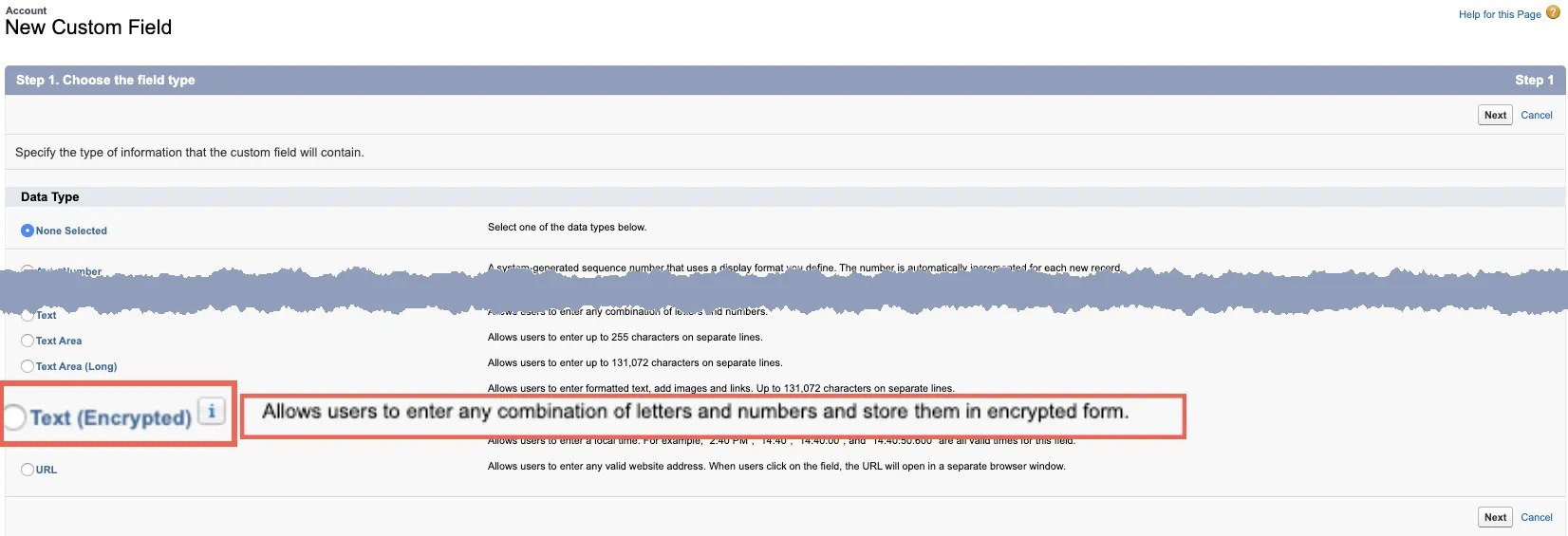
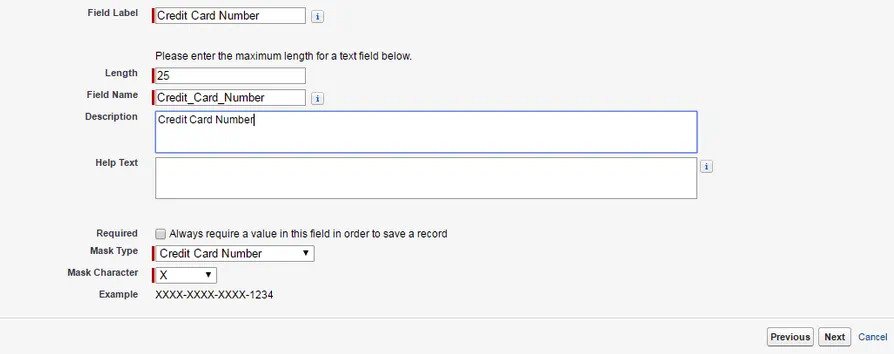
Shield Platform Encryption
Shield Platform Encryption enables you to secure your most sensitive data at rest natively across all Salesforce apps. Encrypting data at rest offers another degree of security to personally identifiable information, and sensitive, confidential, or proprietary data. It also assists you in meeting external and internal data compliance regulations while maintaining important app functionality like search, workflow, and validation rules. You retain complete control over encryption keys and can configure encrypted data permissions to keep sensitive data safe from unauthorized users. See Shield Platform Encryption for further information.
![]() Don’t forget to check out: Salesforce Shield Platform Encryption Guide
Don’t forget to check out: Salesforce Shield Platform Encryption Guide
How Does it Work?
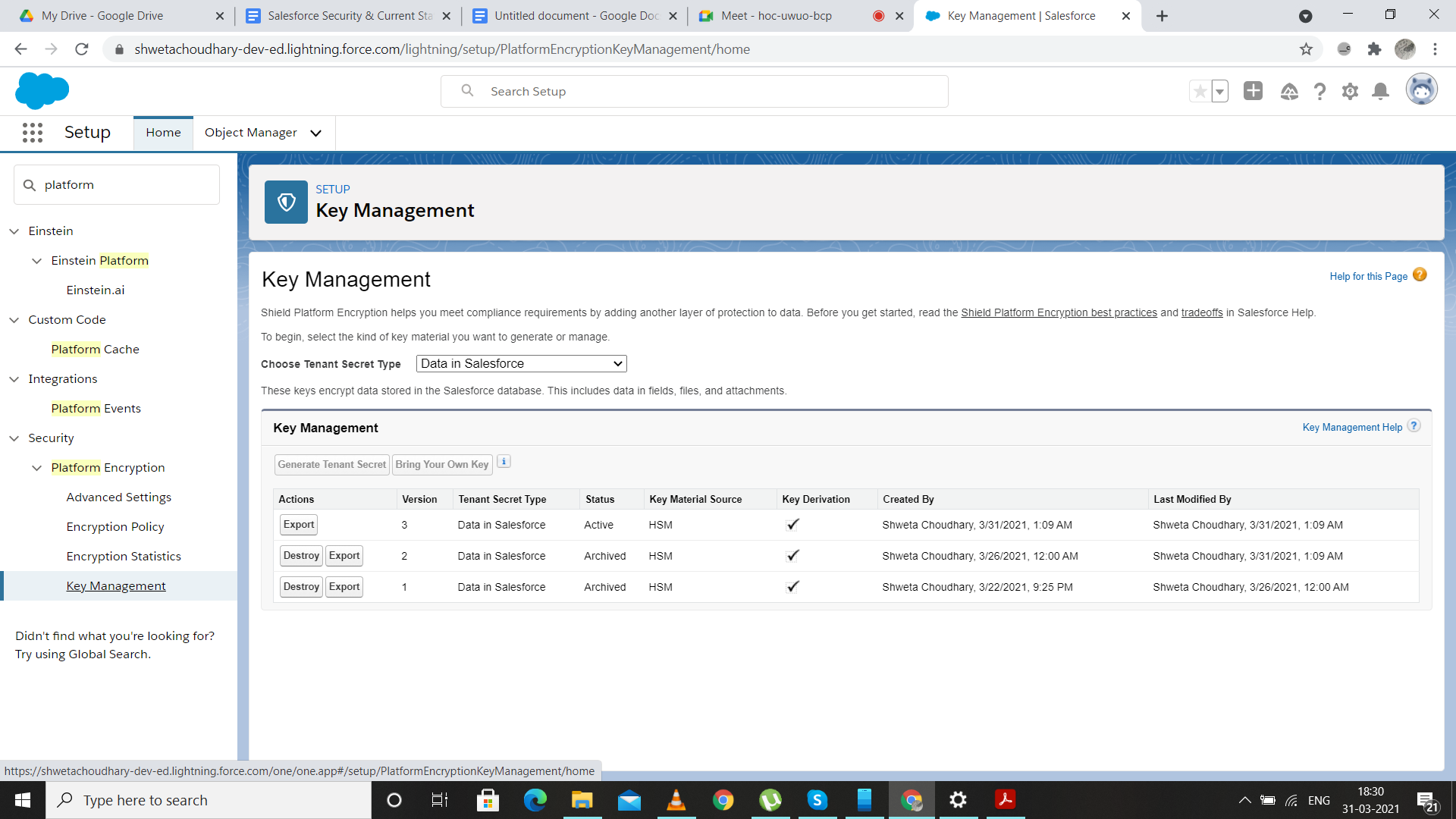
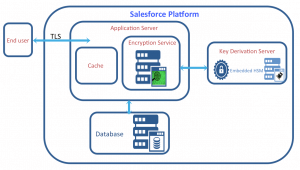
- Customers can generate their tenant secret and encrypt fields, files, and attachments using declarative methods, which require no additional hardware or software.
- Data is encrypted at the application layer, allowing essential features like global search and validation rules to function properly.
- To ensure strong security, the architecture employs full probabilistic encryption and 256-bit AES symmetric keys behind the scenes.
- Clients have complete control over the lifecycle of their HSM-derived tenant secret and can rotate, export, and destroy secrets as needed to meet compliance needs.
- Bring Your Own Key (BYOK) enables clients to offer their own tenant secrets created by their own HSMs, giving them greater control over their encryption processes.
Pricing: Encrypt sensitive and regulated data at rest natively across your apps. 20% of net expenditure
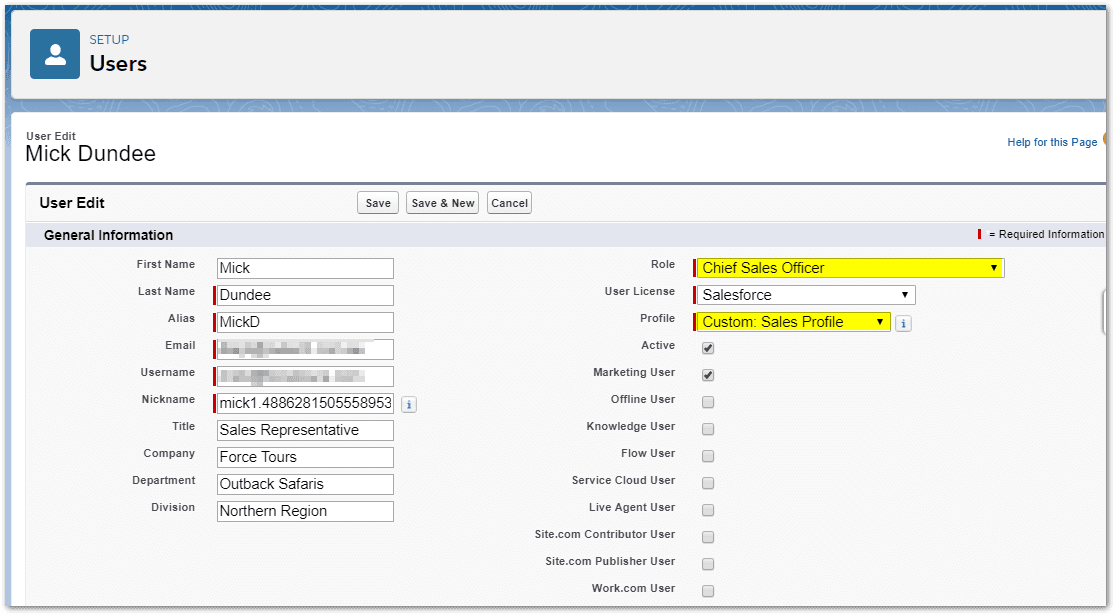
Monitoring of Events in Real Time
Real-Time Event Monitoring provides extensive performance, security, and usage information for all your Salesforce apps. Determine who, when, and from where vital company data is accessed. Learn about user adoption in your apps. To improve end-user experience, troubleshoot, and optimize performance. The API tracks Event Monitoring data, which can be imported into any data visualization or application monitoring tool, such as Analytics, Splunk, or New Relic. Check out our Event Monitoring training course to get started.
How does it Function?
Event Monitoring includes over 40 different event types that describe each of your users’ activities in Salesforce, as well as Einstein Event Monitoring Analytics, which includes 16 pre-built dashboards to help you get started quickly working with event log files and identifying anomalous user behavior.
API access to event log files enables you to analyze and display events in your preferred tool, and powerful AppExchange apps can help you extend functionality and uncover new insights. Data from Event Monitoring is easily integrated into data visualization and application monitoring solutions such as Einstein Analytics, Splunk, Fair Warning, and New Relic. Transaction Security, a component of Event Monitoring, enables you to use clicks to establish security policies implemented in real-time by a configurable and customizable policy engine.
- Track report exports by profile, role, or user
- Track report runs, including those that were not saved
- Track files evaluated, downloaded, and shared with other users
- Monitor bulk, SOAP, REST, and metadata API access
- Identify login compromise
- Get use notifications
- Restrict user actions based on customizable policies. Determine performance issues for custom Visualforce pages, Apex classes, reports, and more.
Pricing: Protect your environment by analyzing performance, security, and usage statistics. 10% of net expenditure
Field Audit Trail
Using Field Audit Trail, you can see the current status and value of your data for any date and time. It can be used for regulatory compliance, internal governance, auditing, or customer service. A field Audit trail is designed on a big data backend for huge scalability and can be used to construct a forensic data-level audit trail. See Field Audit Trail.
How Does It Work?
- Automate field retention – specify standards and rules for what field data is stored, how long it should be kept, and when it should be archived.
- Keep field history data for up to 60 fields per object and up to 10 years. Get rapid access at vast scale — query performance of less than 120 seconds — to quickly assess the state and value of your data for any date.
- Capture your data’s whole lifecycle – field history data is retained, archived, and removed when no longer required.
Pricing: Understand the state and worth of your data and keep it for up to ten years. 10% of net expenditure
![]() Check out another amazing blog by SP here: A Guide to Listing App or Product on Salesforce AppExchange
Check out another amazing blog by SP here: A Guide to Listing App or Product on Salesforce AppExchange
Data Detection by Einstein
You may use Einstein Data Detect to scan your organization for sensitive data and then take steps to protect it. You may speed up data categorization by matching data sensitivity levels and categories to actual field data. Furthermore, you no longer need to rely on third-party services or export your data outside of Salesforce. See Einstein Data Detect for further information.
Locate Learning Resources and Documents Using the Shield Learning Map
The Shield Learning Map is a user-friendly, one-stop shop for everything Shield. The learning map provides a clear path to success regardless of which Shield product you purchase or how you intend to use it. Shield product documentation contains links to the Shield Learning Map.
Become acquainted with Shield by seeing Dreamforce presentations, videos, and overview literature on the landing page. Next, on the trail, you’ll find resources for specific features and use cases, such as developer manuals, how-to instructions, Trailhead, and best practices. The map provides just-in-time information for all stages of your Shield journey, from formulating security policies to putting those policies into effect.
Salesforce Encryption Types for Data Protection
Salesforce offers two forms of Encryption for data protection: Traditional Encryption and Shield Platform Encryption.
The base Salesforce product will include Traditional Encryption capabilities. Therefore, you do not need to pay any more fees. Unfortunately, Shield Encryption requires a license purchase in all orgs to save the developer edition org. Compared to Traditional Encryption, the Shield adds more privacy and security to your data.
Advantages of Salesforce Shield
The main strengths of Salesforce Shield are as simply follows:
- Keep track of performance and event data.
- Encryption can help you meet compliance standards.
- Learn about the worth of your data.
Shield Platform Encryption Tradeoffs and Constraints
Shield Platform Encryption is a powerful security solution that comes with some drawbacks. When your data is encrypted, some users may notice limitations in functionality, and a few features may be unavailable entirely. When developing your encryption strategy, keep your users and the entire business solution in mind.
Best Practices for Shield Platform Encryption
Spend some time identifying the most likely dangers to your organization. This procedure assists you in distinguishing between data that requires encryption and data that does not, allowing you to encrypt only what is required. Keep a backup of your tenant’s secrets and keys and be cautious about who you allow to manage your secrets and keys.
Factors for Shield Platform Encryption in General
These guidelines apply to all data encrypted with Shield Platform Encryption.
Factors for Implementing Deterministic Encryption
These concerns apply to data encrypted using the deterministic encryption algorithm provided by Shield Platform Encryption. Several issues alter depending on whether data is encrypted using a case-sensitive or case-insensitive deterministic encryption technique.
Encryption on the Shield Platform and the Lightning Experience
With a few small differences, Shield Platform Encryption functions in the Lightning Experience the same way it does in Salesforce Classic.
Shield Platform Encryption Field Limits
Encrypting a field can limit the values you can store in it under certain scenarios. We recommend adding validation rules to enforce these field boundaries if you expect users to provide non-ASCII values, such as Chinese, Japanese, or Korean-encoded data.
Which Salesforce Applications Aren’t Compatible with Shield Platform Encryption?
When you operate with Shield Platform Encryption-encrypted data, several Salesforce functions perform as intended. Others, however, do not.
Highlights
Pricing:
- Salesforce Shield is an add-on product, which means it costs in addition to the standard Salesforce CRM licensing types. Shield price is computed as a percentage of your entire Salesforce cost, as opposed to the standard per user, per month pricing, making it a more equitable pricing approach for small-medium businesses.
- Salesforce Shield pricing is up to date and can be seen on Salesforce’s official pricing page.
- Again, you can purchase all four components or each component separately, depending on your regulatory and business requirements.
Salesforce Shield Platform Encryption Offers the Following Benefits:
- Encryption of standard fields, custom fields, files, and attachments.
- Used in workflows and formula fields.
- Provides stronger encryption (256-bit AES) than Salesforce Traditional Encryption.
Salesforce Shield Encryption Drawbacks:
- There is an extra charge.
- Because it does not support masking, Field Level Security (FLS) must be enabled to control field visibility.
- Certain third-party apps are incompatible.
- Included are additional considerations mentioned in Salesforce’s Help Center.
Visit https://trailhead.salesforce.com/ to learn more about Salesforce Shield and how Shield protects business-critical apps and Event Monitoring best practices.