In Salesforce, ensuring that users have the right level of access to data is a cornerstone of both security and efficiency. Roles and Profiles are essential components of Salesforce’s access control model. These tools help administrators manage user permissions, protect sensitive data, and ensure that only the right users have the appropriate level of access to the information they need.
However, many Salesforce admins struggle with understanding the difference between Roles and Profiles, and how to implement them effectively. In this guide, we’ll walk through every aspect of Salesforce Roles and Profiles, exploring why they are essential, how they work, and how they can be optimized to improve your organization’s data security and workflow.
By the end of this guide, you’ll be ready to configure Roles and Profiles that support your organization’s structure and help users get their work done more effectively while keeping sensitive information safe.
What Are Roles and Profiles in Salesforce?
Understanding the core concepts of Roles and Profiles is the first step in mastering Salesforce security. These two elements serve distinct purposes but work together to define what data a user can see and interact with in Salesforce.
Roles: Managing Record Visibility
Roles in Salesforce define record visibility—in other words, which records a user can view. This visibility is typically defined by where the user sits in the organization’s hierarchy. Users at higher levels (like managers or executives) often need to view records owned by users at lower levels (like sales reps or customer service agents).
For example, a regional sales manager needs to see all sales opportunities for their region, while individual sales reps only need access to their own opportunities. Roles make this kind of segmentation possible.
Key Points About Roles:
- Hierarchical: Roles are structured based on the company’s hierarchy. Higher-level roles have visibility into the records of the roles beneath them.
- Not Permission-Based: Roles do not define what actions users can take on records (edit, delete, etc.); they only define what data is visible.
Profiles: Managing Permissions and Object Access
While Roles control what users can see, Profiles control what users can do. Profiles define a user’s ability to create, edit, delete, or view data within Salesforce objects, like Accounts, Contacts, or Opportunities.
For instance, a user with a standard user profile may be able to create and edit their own contacts but may not have permission to delete them. On the other hand, a system administrator with a more powerful profile will have the ability to create, edit, delete, and transfer data across all objects.
Key Points About Profiles:
- Mandatory: Every user in Salesforce must be assigned a Profile.
- Defines Permissions: Profiles control object-level permissions, determining what actions users can perform on different types of records.
![]() Don’t forget to check out: Segments of Salesforce Data Cloud
Don’t forget to check out: Segments of Salesforce Data Cloud
The Role Hierarchy: A Deeper Dive
The Role Hierarchy in Salesforce mimics the structure of your organization, allowing data to cascade down the hierarchy so that higher-level users can access records owned by their subordinates. This hierarchy is customizable, which makes it flexible enough to meet the specific needs of different organizations.
How Does the Role Hierarchy Work?
Salesforce’s Role Hierarchy ensures that data visibility follows the chain of command within your organization. For example, a VP of Sales will have access to records owned by regional managers, and the regional managers will have access to records owned by sales reps in their region.
However, it’s important to note that Role Hierarchy affects record visibility only, not permissions. If a manager has the ability to view a subordinate’s record but doesn’t have the appropriate profile permissions to edit it, they will only be able to view it, not make changes.
Key Features of Role Hierarchy:
- Visibility Without Permissions: Roles only grant access to view records; they do not grant editing or deleting permissions.
- Grant Access Using Hierarchies: A checkbox setting that can automatically extend record visibility to users higher up the hierarchy.
Customizing the Role Hierarchy:
Salesforce allows you to customize the Role Hierarchy to suit your business needs. You can create different hierarchies for custom objects and modify access based on specific organizational requirements. For instance, some organizations may want their marketing managers to see sales-related records, while others may prefer to keep them separate.
Use Cases:
- Example 1: A national sales director needs access to all regional sales data to analyze performance.
- Example 2: A service manager needs to view customer cases for a specific region, but not across the entire company.
Profiles: Controlling Object-Level Security
Profiles are the core of Salesforce’s object-level security model. A profile defines a user’s ability to interact with Salesforce objects (like Contacts, Leads, or Accounts). Every user is assigned a Profile that determines what they can do within Salesforce, from creating and editing records to accessing specific apps or fields.
Key Components of Profiles:
Profiles consist of several settings that allow administrators to tailor permissions for specific user groups:
- Object Permissions: Define which objects a user can access (e.g., Contacts, Opportunities). These permissions control whether a user can create, read, edit, or delete records within that object.
- Field Permissions: Allow administrators to control what data users can view or edit at the field level within an object. For instance, users may be able to view an Account’s name but not its financial information.
- Tab Visibility: Control which tabs and apps users can see in Salesforce.
- Record Types: Assign record types that specify different business processes (e.g., Lead vs. Opportunity processes).
- App Permissions: Define which apps users can access.
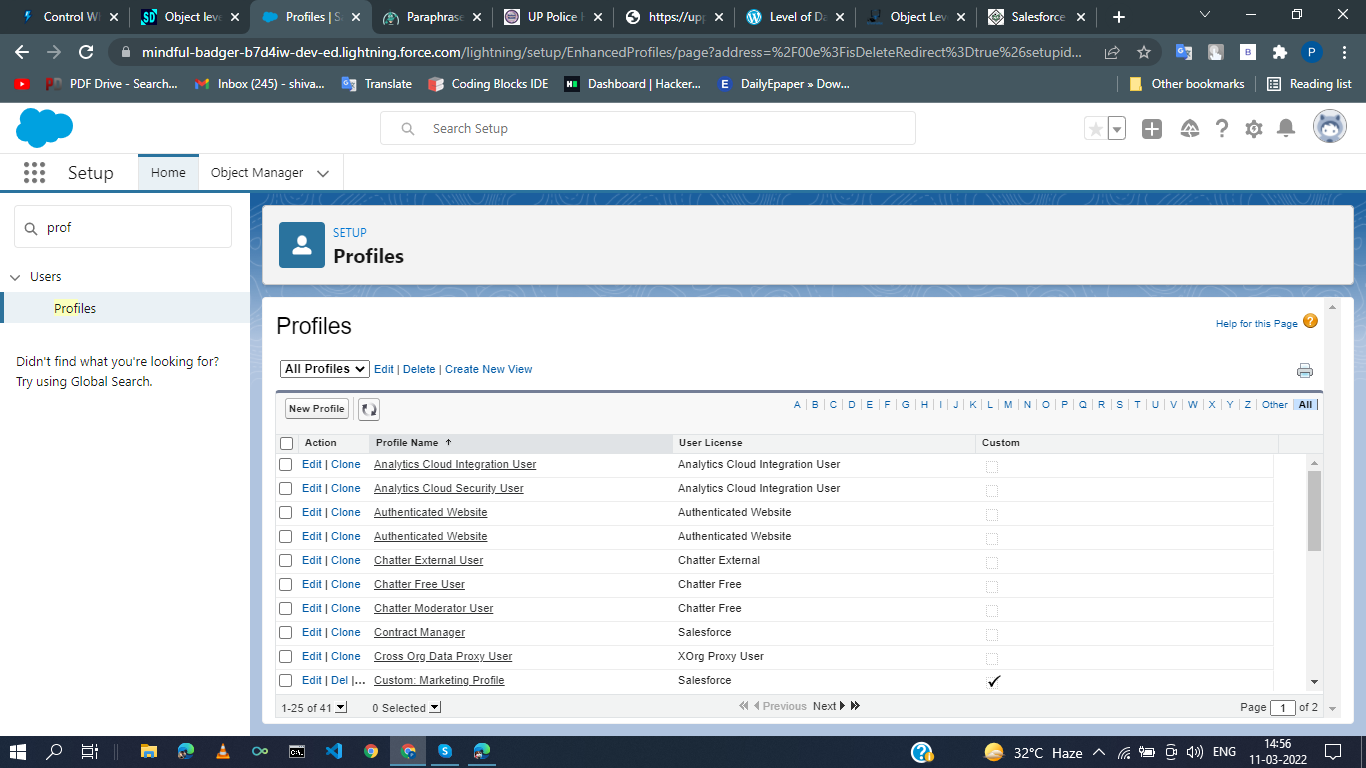
Standard vs. Custom Profiles:
Salesforce provides Standard Profiles for common roles such as System Administrator, Standard User, and Read-Only User. These profiles come with predefined permissions that meet the basic needs of most organizations.
Custom Profiles, on the other hand, offer more flexibility. Custom Profiles allow administrators to define unique permission sets for different users, tailoring the user experience and security model to the organization’s specific needs.
Key Differences Between Standard and Custom Profiles:
- Standard Profiles: Predefined by Salesforce and apply broadly.
- Custom Profiles: Created by admins to meet specific needs and workflows within the organization.
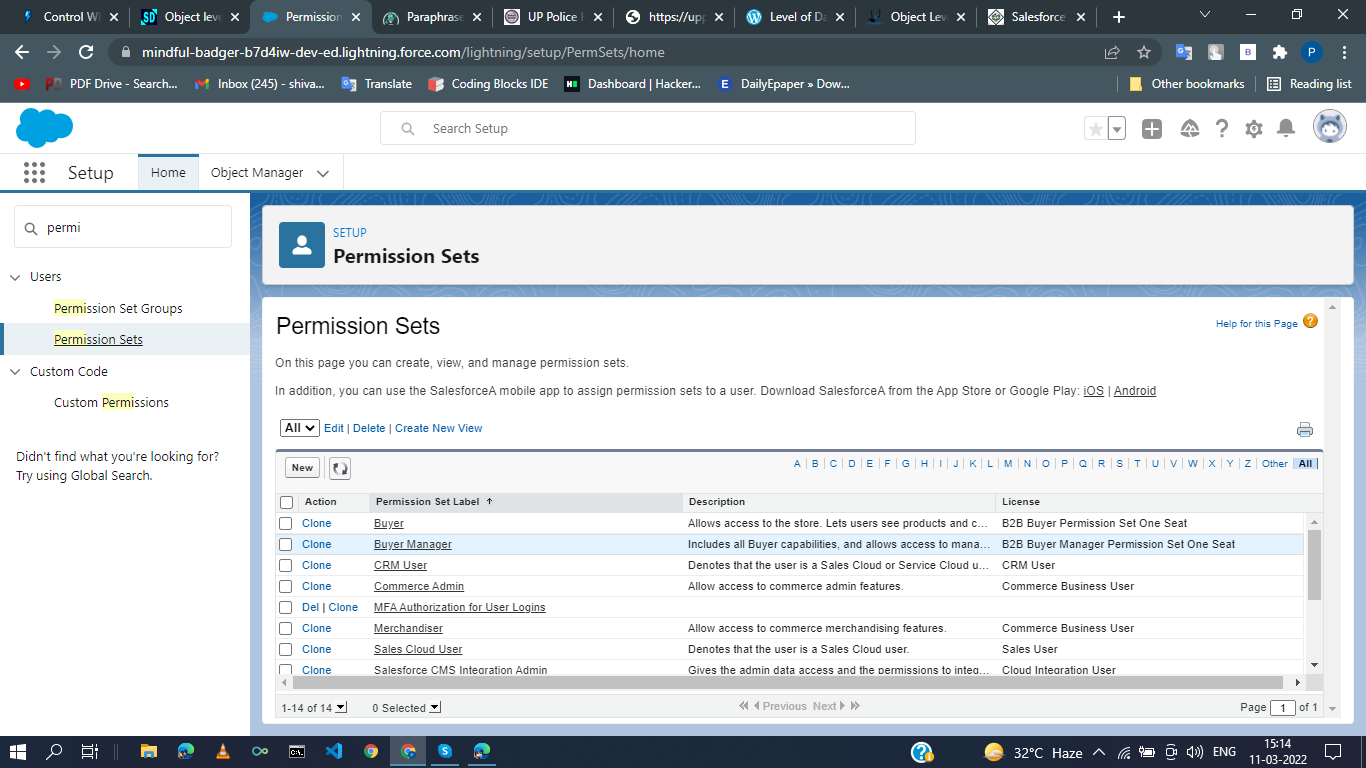
Profiles vs. Permission Sets: Key Differences
One common question is the difference between Profiles and Permission Sets. Both are used to manage user permissions, but they serve different purposes.
Profiles: Setting Baseline Permissions
Every user must have a Profile. Profiles are used to set the default permissions that apply to a user, including access to objects, apps, and tabs. For example, a sales user may have a Profile that allows them to create and view Contacts but restricts their access to the Financial Information object.
Permission Sets: Granting Additional Access
Permission Sets are used to extend the permissions granted by a Profile. They are especially useful when certain users need access to additional features or objects, without altering their Profile. For instance, if a user in the Sales department needs temporary access to a new app, a Permission Set can grant them access without changing their baseline Profile.
Use Cases for Permission Sets:
- Temporary Permissions: Grant a user temporary access to specific features without changing their profile.
- Overlapping Permissions: Give users with different profiles the same additional permissions.
Combining Object and Record-Level Security
Understanding how Roles and Profiles interact is key to mastering Salesforce’s security model. While Roles handle record-level security, Profiles manage object-level security.
Object-Level Security (Controlled by Profiles)
Profiles define object-level security, determining which objects users can access (e.g., Accounts, Contacts) and what actions they can take (e.g., create, edit, delete). Object-level security applies across all records within an object.
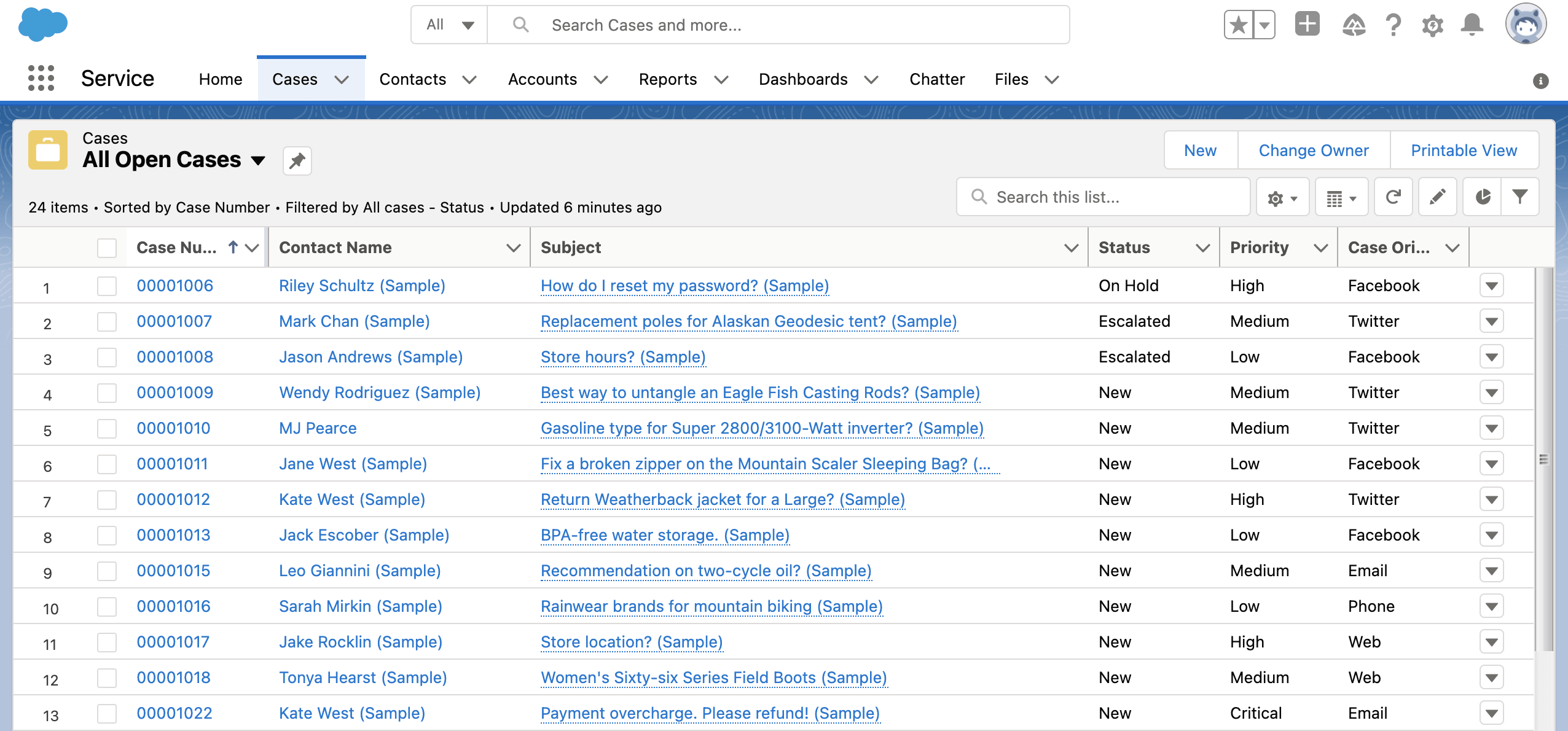
Record-Level Security (Controlled by Roles)
Record-level security is managed by the Role Hierarchy and Sharing Rules. It ensures that users only have access to specific records, based on their Role in the organization.
Examples:
- Scenario 1: A sales rep can create and view opportunities they own (object-level security), but they cannot see opportunities owned by other reps (record-level security).
- Scenario 2: A sales manager can see all opportunities in their team, even if they didn’t create them (role-based access).
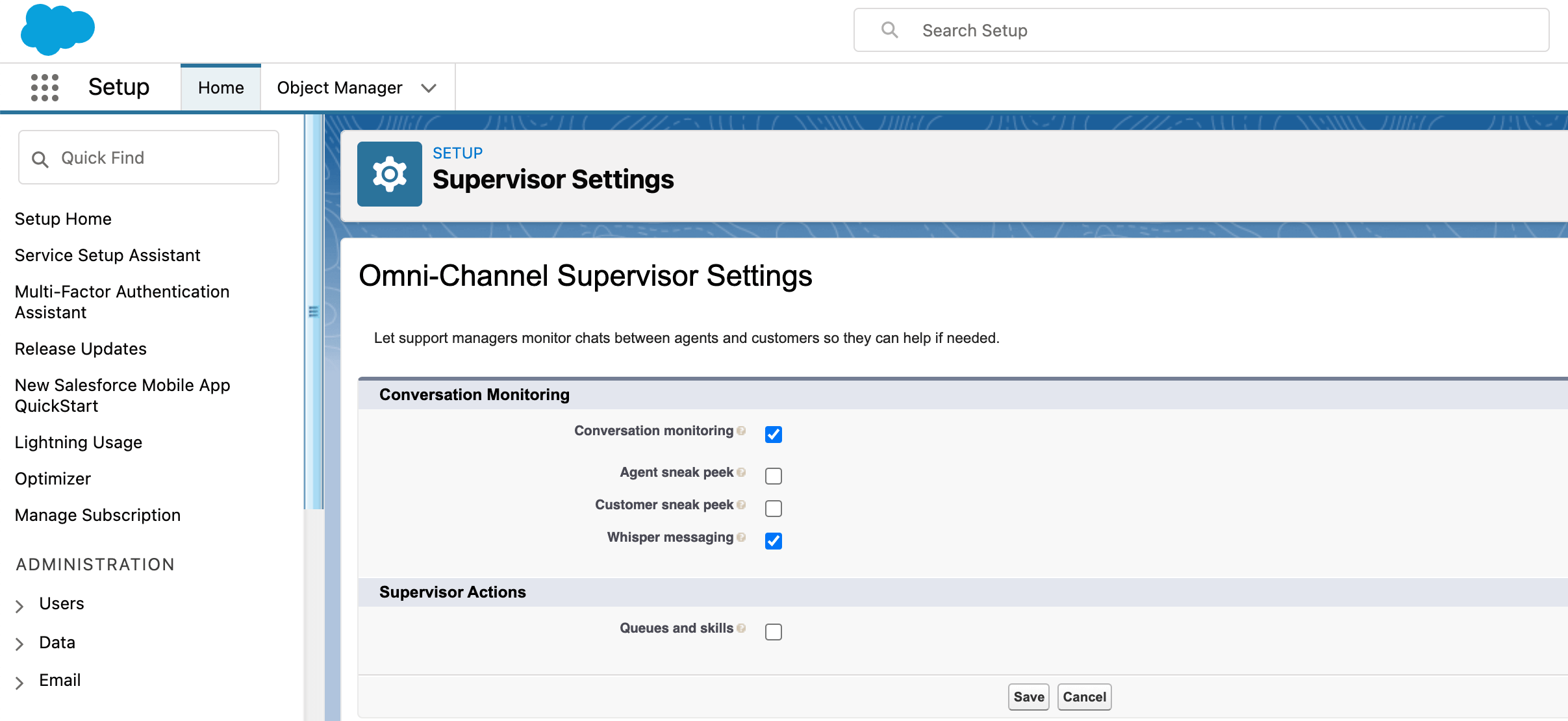
Additional Security Features in Salesforce
Salesforce provides a range of tools to further enhance security beyond just Roles and Profiles. Here’s a brief overview of the key features that help you fine-tune access control:
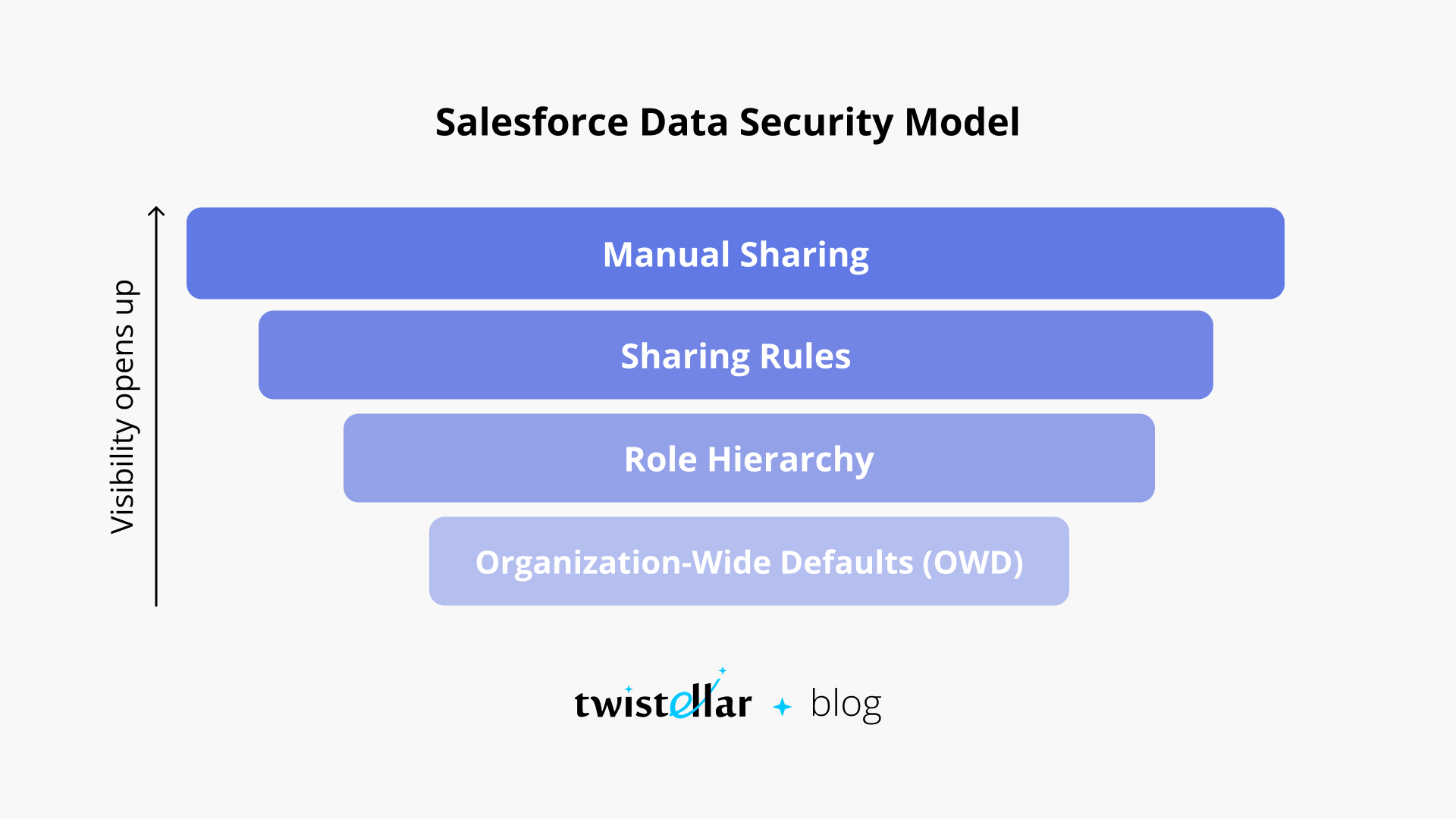
Org-Wide Defaults (OWD)
Org-Wide Defaults (OWD) define the baseline level of access for records across your organization. For example, OWD can make all Accounts private, meaning that users can only see the records they own unless other sharing settings (like Role Hierarchy or Sharing Rules) allow broader access.
Sharing Rules
Sharing Rules enable administrators to define exceptions to the Org-Wide Defaults. For instance, you can create a sharing rule that allows users in a specific role to access records owned by another team.
Manual Sharing
In some cases, users may need to manually share records with others. Manual Sharing allows individual users to share specific records with other users or roles.
Record-Level Security: Enhancing Data Control
While Profiles determine what actions users can take on objects, Salesforce’s Record-Level Security governs which individual records within an object users can access. This layer of security helps Salesforce admins finely control access to sensitive or confidential data based on each user’s role within the organization. While exploring record-level security, you might want to check out our Custom Salesforce Consulting Solutions to understand how advanced security configurations can boost your business operations
Key Components of Record-Level Security
- Org-Wide Defaults (OWD): As mentioned earlier, OWDs define the most restrictive level of access for records. For instance, if the OWD for Accounts is set to private, then users can only access their own Account records unless other sharing mechanisms apply.
- Role Hierarchy: The Role Hierarchy automatically extends access to users higher in the hierarchy, meaning managers or executives can see records owned by their subordinates.
- Sharing Rules: Sharing rules are used to create exceptions to the OWDs, making certain records accessible to users in other roles or groups. These rules are especially useful in cross-functional teams where different departments need to collaborate on certain records.
- Manual Sharing: For scenarios where individual users need to share specific records with others, Salesforce provides the option of manual sharing, allowing users to grant access to particular records.
Use Cases for Record-Level Security
- Example 1: A sales rep can view and edit their own opportunities but cannot view opportunities owned by other sales reps unless they share the same Role in the hierarchy.
- Example 2: A service manager can view and edit customer service cases, but certain cases involving sensitive information (e.g., financial disputes) may have restricted visibility to only a select group of users, even within the same team.
Field-Level Security: Fine-Tuning Access to Specific Data
Beyond object and record-level security, Salesforce offers Field-Level Security to control access to individual fields within an object. This ensures that sensitive information, such as financial data or social security numbers, is only visible to users with the appropriate permissions.
Configuring Field-Level Security
Administrators can configure field-level security to restrict or grant access to specific fields within a Salesforce object. This can be done through Profiles or Permission Sets, ensuring that only users with the correct permissions can view or edit sensitive fields.
For instance, a sales rep might be able to view the contact information for a customer but may not be allowed to see fields related to contract value or payment details, which would only be visible to users in the finance department.
Use Cases for Field-Level Security
- Example 1: Only managers can view and edit the “Salary” field for employee records, while lower-level users have access to other non-sensitive fields like “Name” and “Department.”
- Example 2: In a health-related Salesforce implementation, only healthcare professionals with specific permissions can view a patient’s medical history, while other team members may only have access to non-confidential information like patient name or appointment details.
Object-Level Security: Restricting Access to Entire Objects
Object-Level Security is the broadest form of security within Salesforce, allowing admins to control access to entire Salesforce objects (such as Accounts, Contacts, Opportunities, or Cases). Object permissions are defined primarily by Profiles and Permission Sets, and they determine what actions users can perform on different objects (create, edit, delete, view).
Best Practices for Object-Level Security
- Default to the Least Privilege Principle: When assigning object-level permissions, it’s a best practice to give users the minimal permissions they need to perform their job. For example, if a user only needs to view records, their Profile should not include permissions to edit or delete them.
- Use Permission Sets for Specific Access: If some users require access to certain objects or functionalities only occasionally, it’s best to use Permission Sets to grant this access, rather than creating a new Profile for every exception.
Common Scenarios for Object-Level Security
- Example 1: A marketing user may have access to the Lead object but not the Opportunity object, which is primarily used by the sales team.
- Example 2: Finance users may have read-only access to Accounts but full access to custom objects related to financial transactions and reports.
![]() Check out another amazing blog here: How to Become a Salesforce Partner?
Check out another amazing blog here: How to Become a Salesforce Partner?
Standard vs. Custom Profiles: When to Use Each
Salesforce provides Standard Profiles to cover common roles within organizations. However, many organizations find that they need to create Custom Profiles to meet specific business requirements or workflows. This section delves into the differences and when to use each.
Overview of Standard Profiles
Standard Profiles include common roles such as:
- System Administrator: Full access to all objects, settings, and data in the Salesforce org.
- Standard User: Basic access to standard Salesforce objects, with permissions to create, view, edit, and delete records.
- Read-Only User: Can only view records and reports, without permissions to edit or create new data.
- Solution Manager: Manages solutions in the Service Cloud, including access to case records and knowledge articles.
Benefits of Using Custom Profiles
Custom Profiles are ideal when your organization’s workflow or access needs don’t perfectly align with Salesforce’s predefined profiles. Custom Profiles allow administrators to fine-tune access and create specialized roles that match the nuances of their business processes.
Key Advantages of Custom Profiles:
- Tailored Permissions: Custom Profiles allow you to assign permissions that perfectly match your organization’s structure.
- Specific Workflows: If your company has unique workflows that involve specialized access, Custom Profiles can be designed to streamline these processes.
- Granular Security: Custom Profiles provide the ability to control object, field, and app access at a more granular level.
Frequently Asked Questions About Salesforce Roles and Profiles
Q1: What is the difference between Roles and Profiles in Salesforce?
Roles control record visibility, while Profiles control permissions on what actions users can take on records and objects.
Q2: How do I assign a Role and Profile to a user in Salesforce?
You can assign Roles and Profiles to users from their User Detail page in the Salesforce setup.
Q3: Can a user have multiple Profiles in Salesforce?
No, a user can only have one Profile, but you can use Permission Sets to extend additional permissions.
Q4: How do I modify the Role Hierarchy in Salesforce?
You can modify the Role Hierarchy in Setup under Roles, where you can drag and drop roles to restructure the hierarchy.
Q5: What are the benefits of using Permission Sets?
Permission Sets allow you to grant users additional permissions without changing their Profile, providing flexibility for temporary or specialized access needs.
Final Thoughts
Roles and Profiles in Salesforce are essential tools for securing your data and ensuring that users have the right level of access. By carefully configuring these security settings, you can create a Salesforce environment that meets your organization’s specific needs without compromising on data security.
To optimize your Salesforce implementation, it’s essential to regularly review and adjust Roles, Profiles, and Permission Sets based on evolving business requirements. As your organization grows, so too will your need for more fine-tuned access controls, making it critical to stay proactive in managing Salesforce security.
If you’re ready to optimize your Salesforce environment, check out our Salesforce Implementation Services to get expert support on managing roles, profiles, and more.



 Don’t forget to check out:
Don’t forget to check out: